Bugs and Issues
Some users of the Huawei Nova 5T with EMUI 11 going through navigation key disposition issue

At the moment, every Huawei smartphone user wants to upgrade with the latest custom OS, EMUI 11. However, this major update rolling out program is underway.
Something worth mentioning that after installing EMUI 11 every user is not happy or satisfied because they may be facing some issue or like the previous one more. Additionally, in the recent past, we have also heard about some problems with Huawei Nova 5T on EMUI 11.
About device: Huawei Nova 5T smartphone comes with a large display, powered by Kirin 980 processor, 43MP rear quad camera system, 32 selfie shooter, EMUI 9, and more.
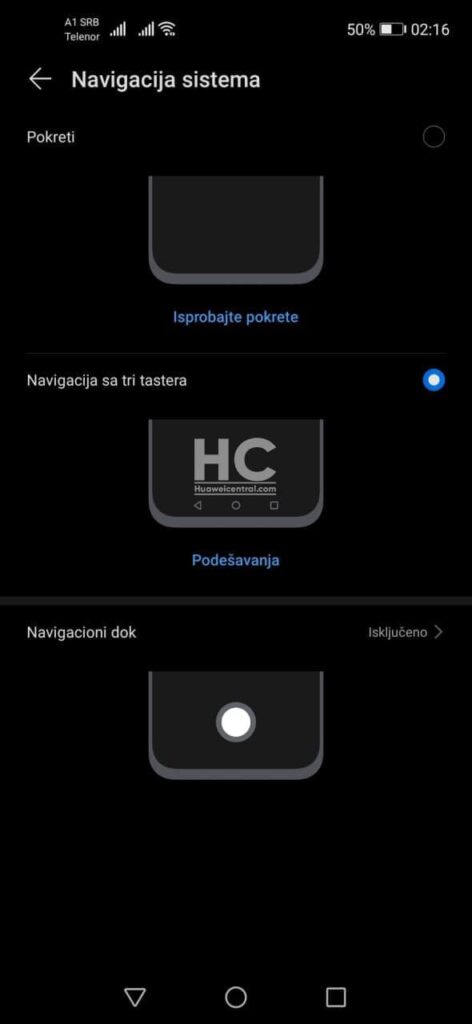
Recently, a Huawei Nova 5T user from Serbia reached us and reported new issues that occur after receiving EMUI 11 version 11.0.0.138 (C431). He said there was a problem with the back navigation key, which remains in the wrong position as shown in the screenshot.
Solution:
Currently, we don’t have an exact patch to fix this issue but if it’s happening because of the EMUI 11. We suggest users contact Huawei support or roll back to EMUI 10.1 version by using the HiSuit app on their PC and Mac.
Warning: This is an official way to roll back to the previous version of EMUI/Magic UI, we recommend you follow the instruction carefully. We’ll not be responsible for any issues that occurred to your device during or after rollback.
We advise users to backup of the important data via SD card, computer, or cloud before rolling back.
Also, check:
Huawei Nova 5T users facing WiFi connectivity and battery drain issue after upgrading over EMUI 11