Bugs and Issues
Are you facing battery draining issue on Huawei P30 Pro after installing EMUI 11?

Huawei P30 Pro is one the best smartphone that was released in 2019 and is the best camera flagship that is ever released by any smartphone maker at that timespan. If we talk about these devices, we can only say one thing – Marvellous!
From its 6.47-inch curved edge OLED panel to the Kirin 980 power center as well as the rear quad-camera system, it allows users to take mesmerizing photos with high-quality as well as Huawei P30 Pro dominates all sections.
That’s not it because it comes with a large 4200mAh battery that supports faster charging at a capacity of 40W featured with Huawei’s SuperCharge technology. Before we dive into our topic, I want to point out the device’s software capabilities.
The Huawei P30 Pro comes with pre-built EMUI 9.1 and the company took good care of the consumers by sending two more major upgrades including the EMUI 10.0, EMUI 10.1, and then EMUI 11.0.
The latest version of EMUI, EMUI 11 comes with a new set of features including smart always-on display (AOD), smoother animation effects in the user interface, and more usability through the latest tweaks made throughout the software system.
EMUI 11 surely brings a number of new improvements for the Huawei P30 Pro and it’s currently expanding for different regions around the globe. However, issues and bugs have no time and date to appear because they just occur and software updates may have the uncertainty of bringing them especially major upgrades.
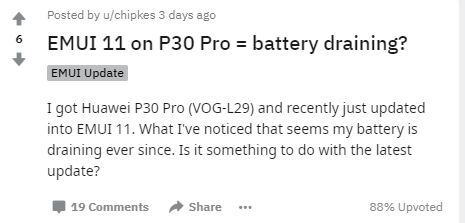
Now, coming back to the topic, there a number of users that reported on Reddit that they’re facing a most common problem with most probability after any upgrade, Battery draining.
According to a Reddit user, the Huawei P30 Pro is consuming more power installing EMUI 11 and mentioned that it wasn’t the case on EMUI 10. In reply to this, some other users pointed out the same mistake, while others mentioned that their units started to provide good battery backup after a few days of using EMUI 11.
Still, the number of users reporting this problem is very limited and not everyone has the same complaints but recently, the Chinese consumers of the P30 Pro stated their encounter with such an issue.
We don’t have any insights into why this issue is occurring but we definitely think it could be related to software optimization. Still, we recommend users switch with a compatible USB and install the EMUI 11 OTA with interruption.
So, it’s time that we hear from you and get your feed on this matter. Are you facing a battery issue on your Huawei P30 Pro after upgrading to EMUI 11? Let us know in the comments.