Bugs and Issues
How to solve common mobile network issue on your Huawei smartphone

Since their invention, there is one common task that every smartphone can perform is to make calls feature using a capability called mobile network. The network on mobile has evolved with time and currently connects to the fifth-gen network or 5G.
Just like any other phone, Huawei phones can also run into a number of network-related issues. The mobile network issue is one of the major problems, it happens when the connection disrupts between SIM card and smartphone. It results in you are not able to receive or make calls, or the 4G network cannot be found on your device.
Below you can check the issues along with their solution to your mobile network issue that you are experiencing on your Huawei device.
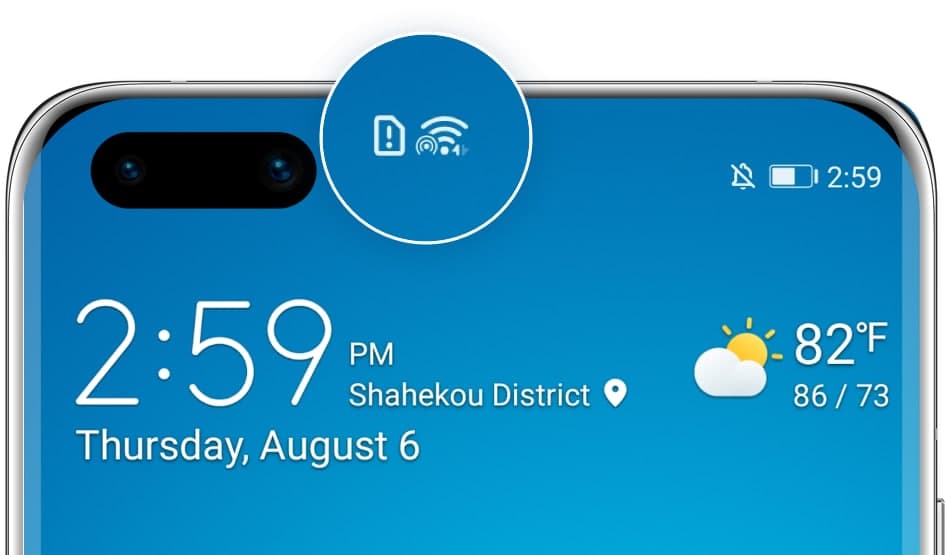
Mobile Network Issue 1: No SIM card found
In this, your smartphone isn’t able to recognize the SIM card that you have inserted into your device.
Steps:
- Takeout the SIM and clear off the dirt on the surface of your SIM card and SIM tray.
- Test your SIM Card on another device to see whether it is damaged. If it does not work on the other device either, please replace your SIM card at your carrier’s retail store.
- If your SIM card can be recognized on another phone, the issue may be coming from your device. In this case, please back up your data and request the Postal Repair Service on the official Huawei Support website or the Support App for a repair.
Notes:
- Please always use standard SIM cards and do not attempt to cut them out on your own, as this may cause poor connection due to nonstandard shapes.
- SIM cards can be damaged by frequently removing them or using them in humid or strong magnetic environments.
Mobile Network Issue 2: Unstable signals
An unstable phone signal might be caused by metal or magnetic materials interruptions or enclosed environments. If you are facing an unstable signal problem, please follow the following step:
- Remove any magnetic holder, or magnetic or metal cases that you may be using for your phone.
- If you are inside a building with a poor signal, please go outdoors or move until you find a better signal.
Mobile Network Issue 3: No 4G signals found
If your 4G signal might be disabled or lost under certain circumstances. Check out the below instructions to resolve this issue.
- Swipe down from the top of the screen to open the notification panel
- Press and hold the Mobile Data icon to enter the settings interface
- Turn on 4G network.
Note: If there is no relevant option, it means 4G is turned on by default.
Also, try this:
- Restart your phone or switch on and off the Airplane mode
- Enable 4G again.
Note: If other phones using the same carrier in the same area have similar issues, it probably means that the local 4G network signal is generally weak and unstable.

Additionally, if you are fronting any other network problem, please try the methods listed below to get over the issue and enjoy the smooth and speedy connection.
1. Check and reset APN Settings
- Open Settings and search for APN
- Tap Access Point Names (APNs) to enter the Mobile data interface
- Select Access Point Names (APNs)
- Touch on the upper right corner and Reset to default.
2. Reset Network Settings
If the APN reset did not work, try resetting your network settings.
- Open Settings and search for Reset network settings
- Tap on Reset network settings to rest it.
Notes: Resetting network settings will delete WLAN and Bluetooth connection records and requires the lock screen password for authentication.
3. Get official support
Find the root cause of the problem with Support App’s Smart Diagnosis feature. To do this:
- Open the Support App
- Click on Troubleshooting and start
Alternatively, get in touch with Huawei through Live Chat on the Support App or the official Huawei Support website.
(Via – Huawei)